AADHAR Database leak has gone more viral in the Dark Web
It is a known fact for heavily curious internet users and security researchers that the Dark Web is place to go to whenever there are new breaches to find or purchase stuff that is not legal and off the grid from authorities. Sometimes these stuffs don’t normally appear on known marketplace sites nor forum sites in the dark web, as there are peer to peer deals where more money can be made than selling it “publicly” on Dark Web markets even if a dark web monitoring team attempts to get the first purchase, marketplace connections will be needed.
This time one of the most coveted data leaks has been spotted in the Dark Web which is quite recently published after the hacking incident last year.
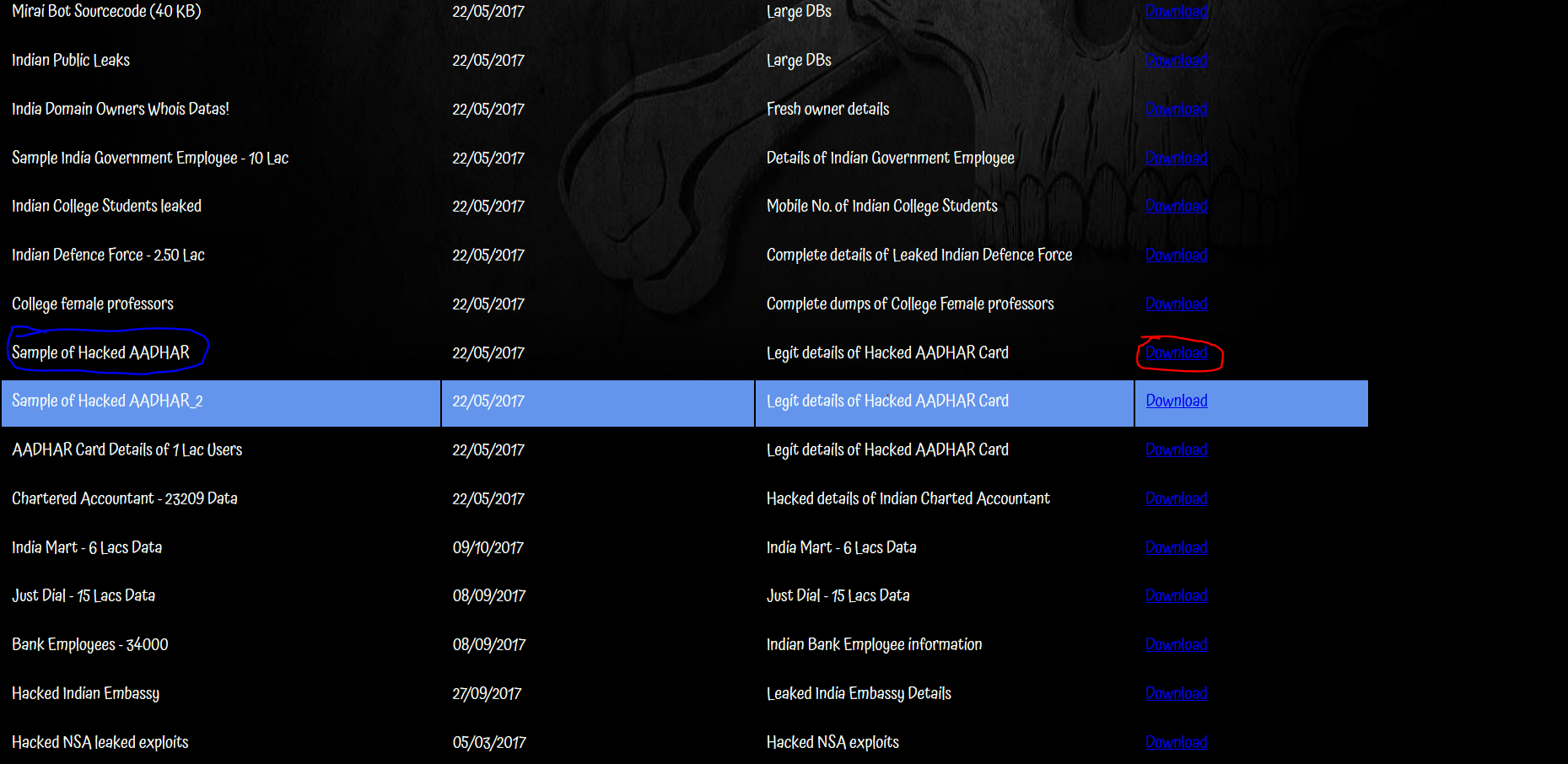
The AADHAR biometrics database has been seen spotted for sale in a darknet site called DIGILEAKS.
What is AADHAR?
Aadhaar is the world’s largest biometric ID system. World Bank Chief Economist Paul Romer described Aadhaar as “the most sophisticated ID programme in the world”
It is a biometric database for residents in India. It may be comparable to USA’s SSN but not entirely, because it is not mandatory. The information stored are only necessary to get benefits from the government.
How was it hacked?
A basic SQL injection method made it possible to hack the AADHAR database through the website.
All the data in the site can be a dump in which why we can now see them on the Dark Web.
Consequence
Stolen biometrics can be incorporated with an illegal modified app to take advantage of the stolen data and then be used for identity theft and then withdraw benefits such as cash and rations that was supposed to be meant for the real owner of the biometrics.
Now that we have witnessed that such data breach can harm victims in such ways security must be properly considered when it comes to dealing with data at all cost.
Hire a decent website developer who has a keen background on security. There is no such thing hack proof, but one can minimize the chances of getting a website hacked.
Dark Web monitoring is also a good option where an intelligence team who is good in monitoring the dark web can watch over on how far the breach has damaged and affected the users data stored. In that way they pinpoint and protect the users affected in a specific manner, not just a general announcement that they were affected.