A new attack campaign is being promoted by cybercriminals that impersonates the pages of Microsoft Store and Spotify. The attackers aim to distribute malware that steals credit card info and login credentials saved on web browsers locally.
The campaign starts by using website ads that appear legit and will lead to a page where the victim can download the malicious application. One of the discovered ads used on the attack campaign that seems to promote an online Chess application as seen below:
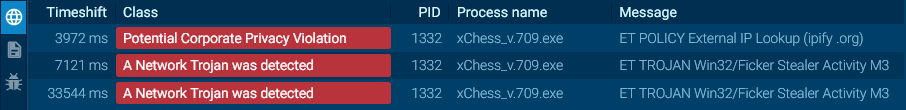
The victims are brought to a fake Microsoft Store page of the application after clicking the ad. A compressed file named “xChess_v.709.zip” will be automatically downloaded from the hacker’s Amazon AWS server hosting. The zip file contains the disguised Ficker or FickerStealer info stealing malware that, once executed, will greet the victim to an online Chess application. The Ficker malware will start to run and start stealing the stored data and cache from the victim’s workstation.
Another campaign ads that contain the Ficker malware leads to a fake page that looks like a legitimate Spotify page or a document converter web app. Once clicked and taken to the landing pages, the automatic download of the trojan zip file will also get triggered.
The Ficker malware is an information-stealing financial trojan released on Russian language hacking forums since January this year when the author started to rent out or offer it as a service to other threat actors. The author allows the rent of the malicious software to anyone from a week up to six months.
With this malware, other hackers can steal saved credentials on web browsers, messaging clients (such as Steam, Discord and Pidgin), exfiltrate documents and take screenshots of the active apps running on the workstation of the victim.
The malware will then compile the data collected into a zip file and transmit it back to the attacker to use it for fraud and malicious activities.
Due to this malware’s broad functionality, the victims of this attack campaign must immediately update and change their online credentials, scan firewalls for port forwarding rules and perform a full scan of reputable antivirus and antimalware tools clean the infected workstation.